I’ve upgraded my lab to 25.1 and have found that the Let’s Encrypt certs aren’t working as expected. I don’t see errors in Firefox or Chrome but code to check the certs are failing against 25.1 with the error “ Certificate validation error: FQDN-25.1 [unable to get local issuer certificate]” which lead me to test with curl.
I’m wondering if anyone else is seeing the same issue or is this something I’m doing wrong.
This is the error I see with “curl -v https://FQDN/”:
root@bam:~# curl -v https://FQDN/
* Trying 10.0.10.26:443...
* Connected to FQDN (10.0.10.26) port 443 (#0)
* ALPN: offers h2,http/1.1
* TLSv1.3 (OUT), TLS handshake, Client hello (1):
* CAfile: /etc/ssl/certs/ca-certificates.crt
* CApath: /etc/ssl/certs
* TLSv1.3 (IN), TLS handshake, Server hello (2):
* TLSv1.3 (IN), TLS handshake, Encrypted Extensions (8):
* TLSv1.3 (IN), TLS handshake, Certificate (11):
* TLSv1.3 (OUT), TLS alert, unknown CA (560):
* SSL certificate problem: unable to get local issuer certificate
* Closing connection 0
curl: (60) SSL certificate problem: unable to get local issuer certificate
More details here: https://curl.se/docs/sslcerts.html
I don’t see the error on a 9.6.1 BAM using the same certificate file and key.
If I look at /data/server/conf/server.cert on the 25.1 BAM I just see the local cert. The local and issuer certs are both in the file on the 9.6.1 BAM.
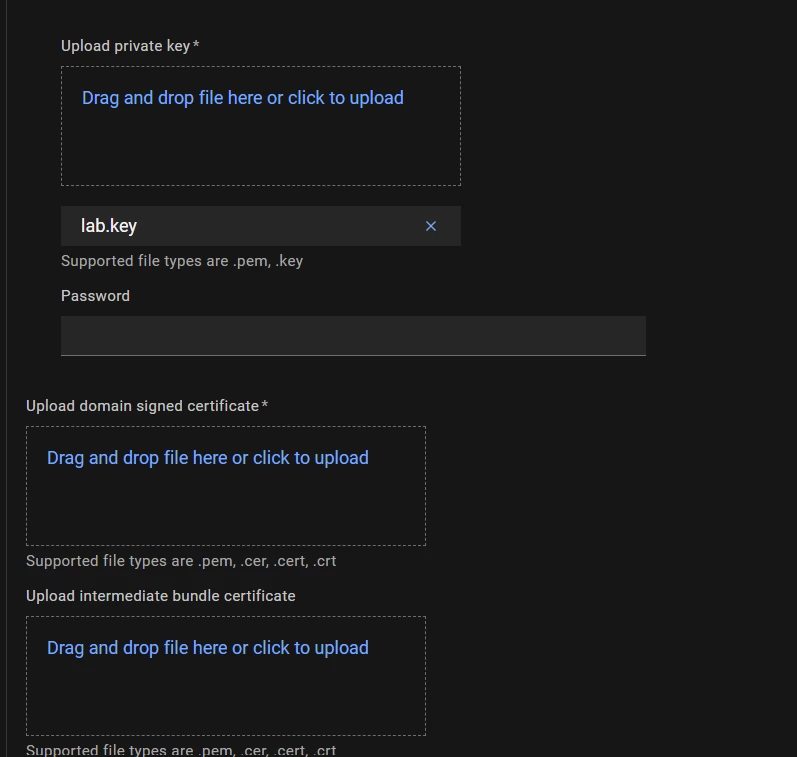
The BAM was upgraded from 9.6.1 to 25.1. After the upgrade I had to load a renewed certificate and that’s when the issue started. I spun up a new 9.6.1 BAM and loaded the new certificate on it to compare.